Why AI in cybersecurity is a double-edged sword

Information moves faster than ever—and so do adversaries. From misinformation campaigns to phishing networks, intense scrutiny of open-source ecosystems like social media is no longer optional for national security teams. It’s mission-critical. At a roundtable discussion with government and industry thought leaders last week hosted by FedInsider.com, Primer’s Skip Farmer delivered a clear-eyed assessment of how proactive threat hunting is quickly becoming table stakes for national security teams. One can't afford to be reactive.
From policy to practice: new cybersecurity mandates
Bad actors—ranging in scope from peer adversaries like China and Russia, rogue nations like North Korea, and even lone wolf cybercriminals—no longer fear directly coordinating attacks in public. They share tactics and timing, identify targets, and now actually brag about successful exploits. Why? Because they know that the volume and complexity of today’s digital ecosystem is a perfect place to hide. For example, in February 2023, the Russian hacking group Killnet publicly announced on their Telegram channel: “We are carrying out strikes on NATO” before launching DDoS attacks that disrupted communications between NATO aircraft providing earthquake relief in Turkey and Syria. The brazen attack targeted humanitarian aid operations, with one C-17 aircraft flying supplies to earthquake victims being directly warned about the disruption during its relief mission.
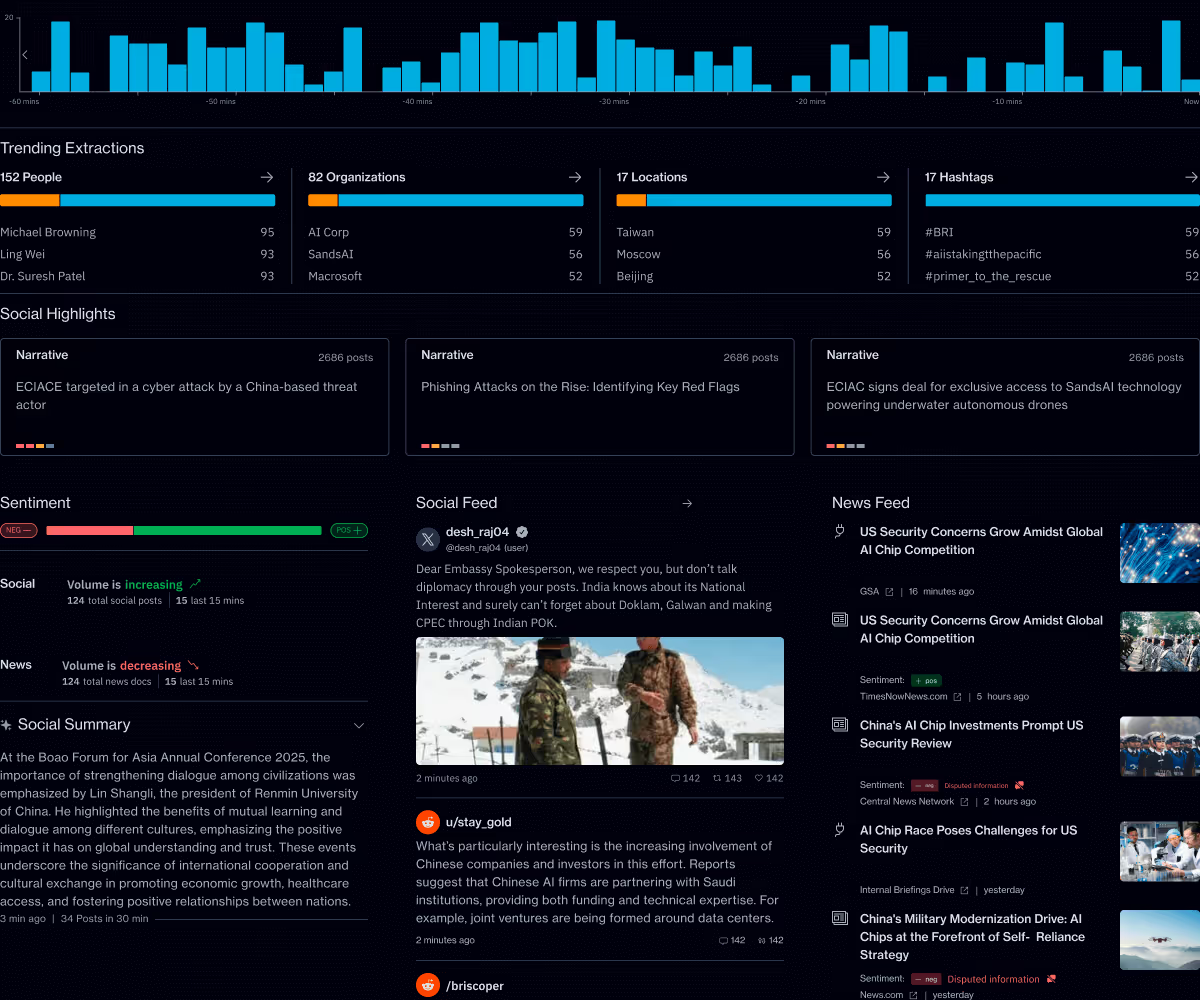
Farmer described today’s challenging open-source intelligence environment as “a massive narrative ecosystem,” where social media posts, community forums, splintering platforms, and 24/7 news coverage blend together into a tornado of information.
This rising threat complexity is echoed at the highest levels of government. A recent White House cybersecurity memorandum—“Sustaining Select Efforts to Strengthen the Nation’s Cybersecurity and Amending Executive Order 13694 and Executive Order 14144” — called for a drastic overhaul on how federal agencies address cyber risks, emphasizing:
- Real-time detection
- Better situational awareness
- Use of automation and AI to accelerate response
The guidance is an important demand signal, urging agencies to equip national security teams with real-time visibility, operational foresight, and the speed to act before threats escalate.
How to find signal through the noise
To detect threats early, Farmer emphasized the need to:
- Extract sentiment, narrative, and behavioral patterns
- Filter out bot networks and coordinated disinformation
- Track narrative shifts across platforms and languages
- Link social and news media signals to real-world impact
The sheer scale of this challenge is staggering—federal agencies must process millions of posts, articles, and communications daily across dozens of languages and platforms, a volume that has already outpaced what even the most skilled human analysts can effectively monitor. In a federal context where the safety and security of hundreds of millions of Americans depends on getting this right, we cannot afford to miss the signals buried in this overwhelming noise. Only AI tuned for national security workflows can handle this level of complexity and volume—especially when lives, missions, and infrastructure are at stake.
AI-enabled threat hunting in action: crypto communities and unexpected threats
Farmer shared a striking example: while monitoring cryptocurrency forums, Primer’s tools uncovered not only scams but emergent physical threats. Soon after, a crypto investor was kidnapped for ransom, targeted for their digital assets. It never would have been caught without the power of AI.What began as online chatter quickly escalated into transnational criminal action. This highlights the need for early detection and rapid analysis—so threats can be stopped before they go operational.
Trustworthy AI built for mission context
Farmer emphasized that it’s not just about having AI—it’s about having the right kind of AI:
- Provenance and explainability are critical. Every alert must be grounded in verifiable data.
- Platforms must support hybrid LLM/SLM architectures and air-gapped deployments for secure environments. Federal agencies often operate across fragmented data ecosystems with varying security classifications, requiring flexible AI systems that can deploy specialized models for different tasks without compromising operational security.
- Multilingual ingestion and structured entity analysis are no longer “nice to have”—they’re essential. Threats don't consider language barriers, and the ability to automatically identify and track entities across communications in dozens of languages can mean the difference between early detection and catastrophic surprise.
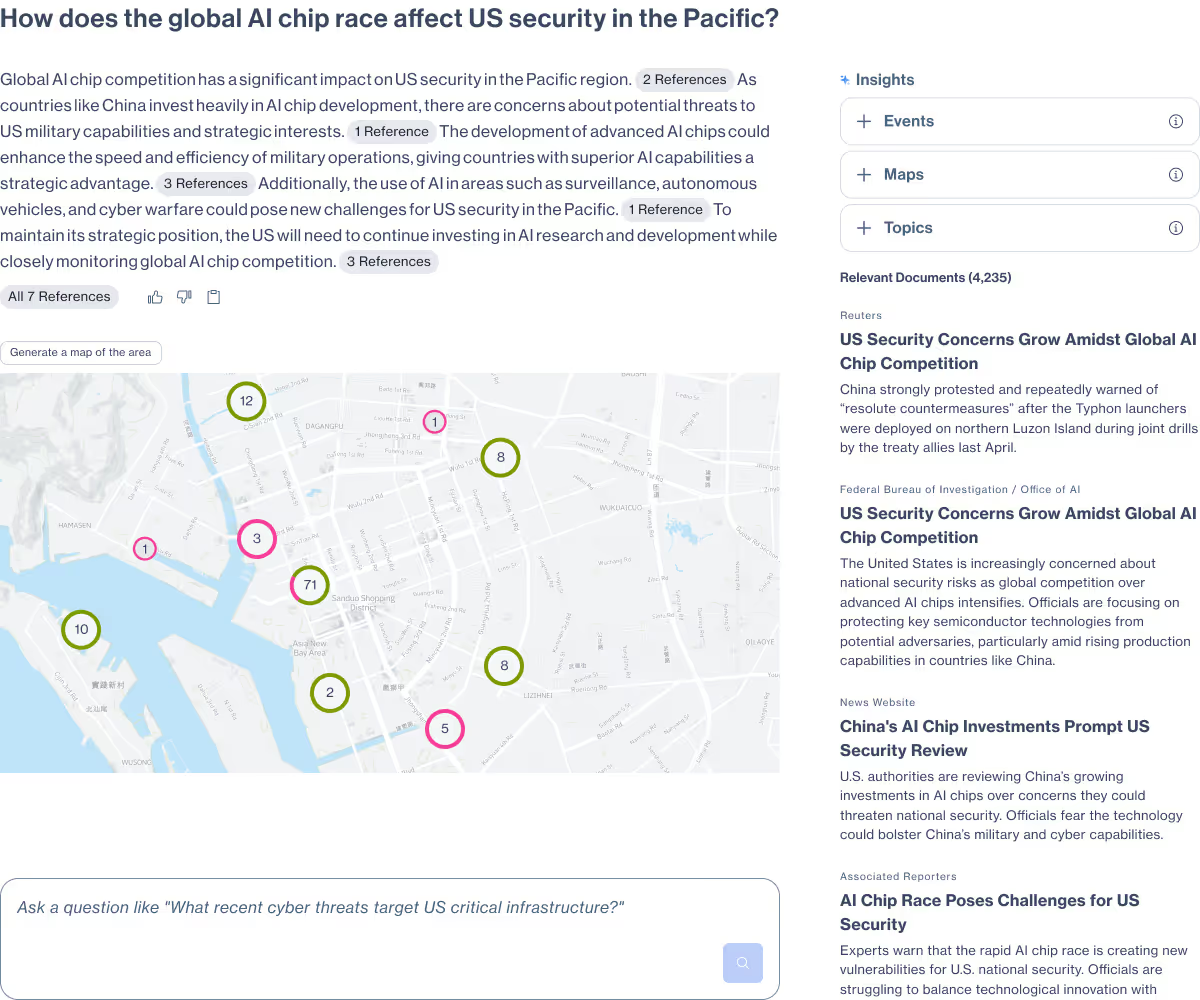
Primer Command and Enterprise deliver exactly this. Built for defense, homeland security, and intelligence use cases, the platform supports:
- RAG-V (Verified Retrieval-Augmented Generation) for trusted, auditable output. Unlike standard RAG systems, RAG-V ensures every piece of generated analysis is grounded in verified, traceable sources that meet intelligence community standards for reliability and attribution.
- Deployed securely—on-prem, cloud, or air-gapped environments. Few AI platforms can operate effectively in classified environments, but Primer Enterprise is designed to deliver full capability regardless of security classification or network isolation requirements.
- Tradecraft-aligned workflows for mission analysts and crisis responders. The platform integrates seamlessly with existing analyst workflows while providing specialized interfaces designed specifically for intelligence collection, assessment, and rapid response scenarios.
- AI-powered visualizations for faster threat detection in high pressure or time sensitive environments. Primer provides intuitive, analyst-friendly visual assets—like timelines, geospatial maps, and network graphs—that help teams make sense of complex patterns across time, location, and entities.
Final word: no shortcuts, no silver bullets
Farmer’s closing thought was clear: AI isn’t a shortcut—it’s a capability multiplier. But only if implemented with forethought, trust, and alignment to operational needs. With threats growing and policy pressure mounting, the ability to monitor, assess, and act in real time has become a baseline expectation.
Explore how Primer Enterprise enables your team to detect and respond to emerging threats in real time—across public data, proprietary networks, and secured missions.
Primer Enterprise
Informed, defensible analysis
Primer Enterprise is a secure AI platform that helps analysts and mission teams across the Intelligence Community, Defense, and Civilian agencies analyze massive volumes of unstructured data. It transforms fragmented reports, proprietary data, and open-source information into structured, traceable insight that supports faster, defensible decision-making.
Primer Command
Real-time operational clarity
Primer Command is an AI-powered monitoring platform that helps mission teams keep track of narratives, track evolving topics, and detect emerging threats across global news and social media. It provides real-time visibility into the information environment so leaders can understand events as they unfold.